Regulatory Compliance Part 2: Industry Regulations and Implementation
- Blog >
- Regulatory Compliance Part 2: Industry Regulations and Implementation
In my previous blog, I looked broadly at the regulatory compliance landscape facing companies today. To build on that foundation, in this article I’ll break down some of the specific regulations organizations in various industries need to take into consideration. Following that, I’ll touch on how these companies can implement regulatory compliance practices to meet the requirements put forth by these regulations.
In the interest of simplicity, this article covers regulations and laws that apply to U.S. companies (some of which may have a global impact). In future articles, we may explore regulations in other regions to expand on this topic.
Regulations and Laws Relevant to Industry
Let’s take a look at some of the industry-specific standards related to finance, technology, and healthcare.
Financial Industry
- Payment Card Industry Data Security Standard (PCI DSS). The four credit card industries define this standard to enhance the translation security of credit and debit cards.
- Gramm-Leach-Bliley Act (GLBA). This federal law requires financial institutions to offer explanations regarding sharing and protecting customers’ information.
- Sarbanes-Oxley Act (SOX). This act refers to financial and auditing regulations for publicly traded companies.
- Financial Industry Regulatory Authority (FINRA). This non-profit corporation efficiently regulates the operations and actions of U.S. financial securities companies.
Technology and Data Security
- Federal Information Security Management Act (FISMA). All federal agencies must keep information technology processes secure from unauthorized access and other data breaches. As a result, these companies should implement the relevant programs and processes to comply with FISMA.
- California Senate Bill 1386. Under this law, if a company gets hacked, it should notify the California citizen whose personal information is leaked during the data breach.
- Consumer Data Protection Act (CDPA). As the name suggests, this act defines a comprehensive framework to control and process the consumers’ data.
- California Consumer Privacy Act (CCPA) – This data privacy law defines the standards for collecting consumer data and the dire consequences for organizations that don’t ensure user data protection.
- Cybersecurity Maturity Model Certification (CMMC). This regulation measures the maturity of cybersecurity practices and internal processes within an organization.
- ISO 27001. One of the leading global standards related to information security developed by different organizations and industries.
- National Institute of Standards and Technology (NIST). Part of the U.S. Department of Commerce, these cybersecurity standards include regulations such as the NIST CSF (Cybersecurity Framework), NIST 800-53, and 800-151.
Healthcare
Both hospitals and healthcare institutions must adhere to the following regulations:
- Health Insurance Portability and Accountability Act (HIPAA). This act protects healthcare workers’ health insurance when they switch jobs. Hospitals can implement the HIPAA framework’s privacy rules to limit disclosure of patients’ information, security rules to maintain confidentiality, and breach notification in case of a privacy breach.
- Joint Commission. A non-profit organization that accredits healthcare organizations and hospitals within the United States.
- Protected Health Information (PHI). This privacy law guarantees federal protection of patients’ health information in the records of the hospitals.
Workplace Regulations
Some regulations apply across all industries and, in some cases, to all U.S. citizens.
Civil Rights
The following laws protect U.S. citizens’ rights:
- Americans with Disabilities Act (ADA). As the name suggests, this law protects the rights of disabled people and prevents any discrimination based on someone’s disability.
- Civil Rights Act of 1964. This law strictly bans and discourages discrimination among citizens based on sex, nationality, religion, and race.
- Personally Identifiable Information (PII). PII refers to the information used to identify, link, or trace someone’s identity.
Workplace and Employment
Whether multi-national or local, small-scale or large, all organizations should adhere to these workplace regulations:
- Family and Medical Leave Act (FMLA). U.S. companies should offer their employees unpaid leave under exceptional circumstances related to medical and family situations.
- Fair Labor Standards Act (FLSA). This law defines the minimum salary and overtime wages for workers.
- Uniformed Services Employment and Reemployment Rights Act (USERRA). Under this law, the members of military reserves enjoy civilian job rights while on duty.
- Workers Adjustment and Retraining Notification Act of 2003 (WARN). Under this act, organizations with 100 or more employees notify the worker 60 days prior to layoffs or company closure.
- System and Organization Controls (SOC2). These internal control reports audit the services offered by the organization to consumers using the organization’s services.
Other Regulations
Other environmental, immigration, and retirement regulations include:
- Hazard Analysis and Critical Control Points (HACCP). This law efficiently addresses food safety issues.
- Migrant and Seasonal Agricultural Worker Protection Act (MSPA). This law protects the housing and employment of the seasonal farmers of the U.S.
- Employment Retirement Income Security Act (ERISA). This law defines the employee benefit plans within the U.S.
- International Traffics in Arms Regulations (ITAR). This law regulates, controls, and restricts the export of defense and military technologies.
Agencies Offering Guidance on Regulatory Compliance
The following agencies and working groups define and administer the regulations mentioned above:
- The US Securities and Exchange Commission (SEC) defines and regulates the laws regarding U.S. securities and publicly traded companies.
- The US Office of Foreign Asset Control (OFAC) imposes trade sanctions on organizations and foreign governments.
- The Small Business Administration (SBA) offers information to help different organizations understand the regulations that apply to them.
- The Environmental Protection Agency (EPA) defines laws regarding operations that impact the natural environment.
Implementing Regulatory Compliance
Organizations must devise and implement an effective regulatory compliance procedure to comply with the myriad regulations affecting their operations. The very first step is to create awareness amongst employees by conducting training programs regarding the importance of regulatory compliance.
The next step is to conduct a compliance audit to determine the risks, data breaches, and other quality assurance issues within the organization to determine a compliance baseline from which to operate. Hence, the relevant teams or hired consultants can perform an analysis to determine the strengths, weaknesses, opportunities, and threats of the security policies and risk management processes in place.
Next, the company can identify compliance gaps and other problematic areas to implement best industrial practices. It’s the primary responsibility of the Chief Compliance Officer (CCO) to define the company-wide policies and processes to address compliance areas identified in the audit. It is the responsibility of your Chief Information Security Officer (CISO) to ensure that each of the technology systems you have adhere to these stringent guidelines. Together, these two executives need the tools and technology necessary to meet these business requirements.
It’s essential to review all these policies relevant to your business regularly to mitigate risks and other data breach possibilities. Furthermore, the compliance team should periodically update employees regarding the changes in compliance policies and requirements to ensure each employee is adhering to the items necessary to meet your needs.
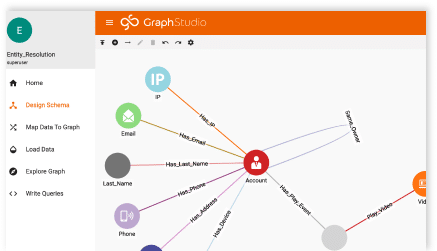
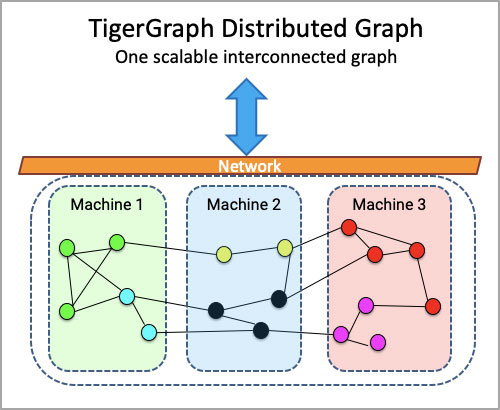
The biggest area lacking in each organization though is visualization. Are you conducting regular attestations? Are you scanning for the threats or use of private data in a way that could be putting your business at risk? Visualization using graph technology can help you ensure you’re meeting your requirements and providing the level of automation necessary to help your team stay on top of all threats throughout your organization.
Final Thoughts on Regulatory Compliance
Successful business leaders understand that regulatory compliance is a continuously evolving process requiring regular reviews, audits, and training. That’s why all organizations should consult with and hire experts to help meet each of these regulatory requirements.
This two-part blog series is intended to help you understand the regulatory requirements facing your organization and others like yours. While technology is almost never the sole answer to successful compliance, graph database technology – like TigerGraph – can give you the edge in achieving proper reporting, monitoring, and visualization to make your regulatory compliance a strength, not a liability, to your company’s continued success.