Understanding the Cybersecurity Threat Social Media Poses to Your Enterprise
- Blog >
- Understanding the Cybersecurity Threat Social Media Poses to Your Enterprise
Enterprise cybersecurity programs are tasked with protecting the company’s data and limiting the impact of data breaches. But, when you think about cybersecurity, do you think about the effect social media can have on enterprise security?
A prominent social media presence is virtually a necessity today, but it also can put your company at risk of damage or compromise. Threats from social media may not be immediately evident, but they are just as potentially dangerous as any other type of cybersecurity risk.
Identifying your risks and safeguarding your social media accounts will ensure your organization and all of its clients are always protected. In this article, I will cover the most pressing enterprise social media threats you should know about and provide tips on how to prevent them from affecting your business.
Common Social Media Security Threats
While social media platforms provide some measures to protect their users, integrated solutions on their end are not enough to protect your organization. As technology advances, cyberattacks become more complex and difficult to mitigate.
Below are several of the greatest risks facing enterprises on the social media front today.
Spoofing and Phishing Scams
Fake social media profiles are, unfortunately, quite prominent today. These accounts, called ‘spoofs,’ can be fairly difficult to distinguish from the real thing. They may copy your brand’s logo and even link back to your official website. Whether they are mimics of individuals’ accounts or corporate pages, they can cause several problems.
Spoofed accounts allow third parties to send people messages that appear to be legitimate.. They can also send emails that seem official, but actually collect people’s data and compromise personal information. Phishing in this manner takes advantage of the trust your customers have in your brand, making these efforts even more effective.
When people realize their data has been stolen and likely used in harmful ways, the aftermath tends to reflect poorly on your business. In some cases, companies can even have lawsuits filed against them for actions performed by someone else.
Impersonated accounts also allow malicious actors to spread misinformation that can negatively affect your brand’s reputation. In some cases, impersonators may even use their fraudulent accounts to deliberately spread lies and make derogatory comments as your business.
To prevent phishing, ongoing monitoring for lookalike websites, similar domain names, and fraudulent social media accounts is important.
Identity Theft
Thanks to the effectiveness of spoofed accounts, enterprises can wind up unknowingly “competing” with a counterfeit version of their organization online. Imagine if Coca-Cola opened another Instagram account or Twitter profile. Thousands of people would likely follow it and provide personal information to sign up for promotional offers, only to wind up losing their identity to the scammers.
Businesses must always be well-versed in these threats and fully understand the extent of their organizations’ online presence. Actively monitoring their accounts and any potentially similar profiles can prevent identity theft and misrepresentation.
Malware
Enterprises can become infected by malware that mines consumer data and confidential information. Ensure that all employees are using best practices, such as accessing social media through a VPN and never clicking on links in messages that could contain malware.
Private links in any message are often used in scams, so no one should open any link they aren’t 100% sure is safe.
Furthermore, installing the appropriate antivirus and antimalware software on all company computers is crucial to protecting your organization against malware and other viruses.
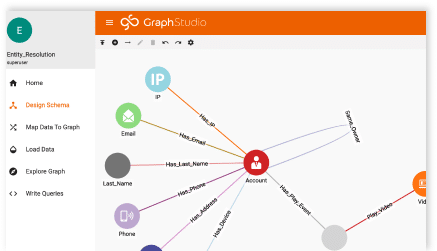
Protecting Your Enterprise Social Media
Bolstering your internal cybersecurity solutions is more important than ever. Providing your team with proper deep link analytics to quickly identify when malicious code has been found or when anomalous activity is happening between devices within your network is critical to the security of your environment, your data, and your customers. With enterprises relying so heavily on social media for marketing purposes, they need the right solutions from trusted partners.
Using platforms that help identify abnormal behavior and flag potential threats to your business online will ensure faster threat identification. Correlating individual events or analyses, though, can significantly slow down your response time and will, in turn, cause you to raise the risk level of activity on your systems. Making the right choices on the solutions you use is strategically important.
TigerGraph provides a level of analysis and analytics that will help in navigating this digital landscape. To further protect your brand, learn more about how our platform is used for cybersecurity threat detection and reach out to us for more information and a demo of our solutions.