How to Find Indirect Sanctions Exposure by Following Connection Paths
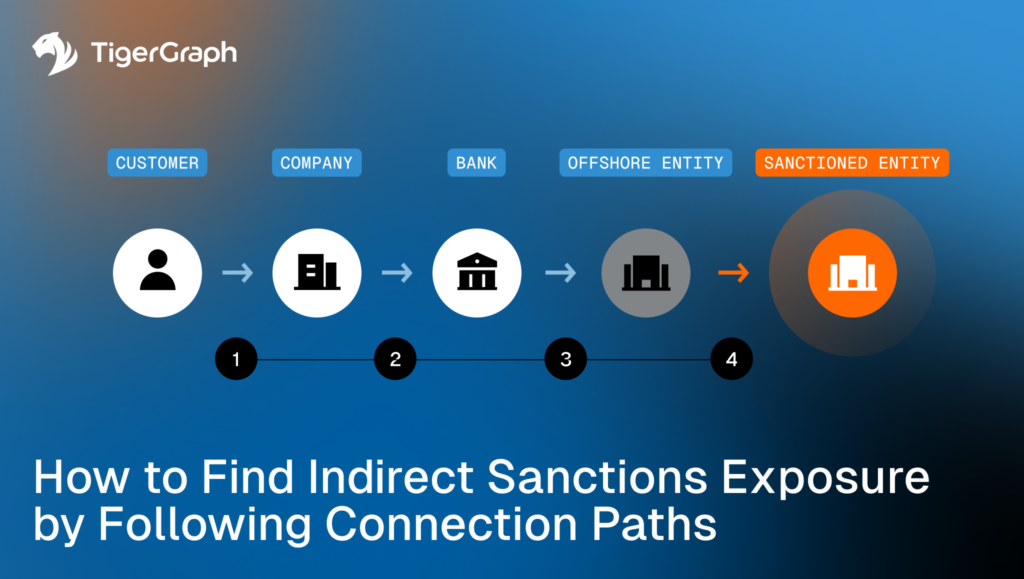
Sanctions exposure often does not show up as a clean match to a name on a list. It shows up one or two relationship steps away, through intermediaries, ownership layers, shared infrastructure, or routing choices that only become clear when you follow the chain.
Direct screening is necessary, but it is limited to what is directly visible. When the exposure sits in the relationships, you need a workflow that can return the path, surfacing the chain of connections used, and preserve it as reviewable evidence.
Key takeaways
- Indirect exposure is commonly missed when screening is limited to direct matches.
- Jurisdiction hopping becomes more meaningful when it appears as an unnecessary path pattern across connected activity, where each hop is one relationship step from one entity to the next.
- Escalation based on connection proximity requires explainable paths, not only scores or isolated alerts.
- Some risk signals emerge only after traversal across relationships. That is a limitation of direct-only screening.
Why Sanctions Exposure is Often Indirect
Real-world financial networks rarely connect cleanly from a customer to a named entity on a list. They include intermediaries, nested relationships, and shared infrastructure that can carry exposure without creating an obvious direct match.
Indirect exposure often appears through connection paths such as these. An intermediary that sits between two parties. A layered chain that adds steps without a clear operational need. A connected neighborhood where an entity is consistently close to flagged activity, even when the entity itself does not match a list.
This is where sanctions screening becomes a relationship problem. The compliance question becomes whether a customer, counterparty, or transaction is connected to exposure through relationships that the program treats as meaningful.
The signals below describe common ways that indirect exposure shows up in the connection chain.
Multi-hop Sanctions Exposure Signals that Matter
These signals are not proof of a violation. They are indicators that exposure may exist and requires review within program policy.
Indirect exposure to sanctioned entities
Exposure can appear through second- or third-degree connections, and sometimes more depending on policy. Examples include intermediary relationships, ownership layers, or shared infrastructure that links an entity under review to a sanctioned entity through multiple relationship steps. The operational requirement is the ability to return the chain that creates the exposure, not only the fact that exposure exists.
Jurisdiction hopping without business justification
Routing through multiple jurisdictions is not automatically suspicious. The signal strengthens when the path includes extra hops that do not appear necessary for the stated activity, especially when similar hop patterns repeat across connected entities or corridors your program monitors closely. In this context, unnecessary hops are best evaluated as a path pattern, not as a single-transaction attribute.
Escalation driven by relationship proximity
Some programs escalate based on relationship proximity. The closer the entity is to a sanctioned entity through relationships that matter to policy, the higher the review priority. This approach requires explainable chains. Reviewers need to see how the relationship was assembled and why it qualifies as exposure under the program definition.
Risk visible only after traversal
Some exposure cannot be seen in a direct match view because the relationships that carry the exposure are not direct. The risk emerges only after expanding through intermediaries, nested connections, and relationship paths that are not known in advance.
What Graph Adds
Graph traversal expands search step by step from one account or party to the next. It supports variable-depth questions where the number of hops is not fixed at the start. A hop is one relationship step from one entity to the next. This matters because sanctions exposure often appears after two or three hops, and sometimes more depending on policy.
Graph workflows also return explainable exposure paths. The chain becomes the escalation rationale, not a black-box result. Reviewers can see the entities involved, the relationship types used, and the hop count that created the exposure.
Path features can be expressed in practical terms. Hop count shows how many steps connect the entity to exposure. Relationship types clarify what kind of connections were used in the chain. This keeps the output aligned to policy and easier to review.
Any weighting logic, such as giving certain relationship types more importance or prioritizing newer connections, should be treated as program-defined unless there is approved language for it. If the program uses weighting, the workflow should still return the underlying path evidence for review.
How TigerGraph Fits
Graph, in general, supports sanctions exposure analysis because relationships are stored directly and paths can be returned as evidence.
TigerGraph fits when teams need to follow relationships at investigation depth and still produce outputs that stay consistent and reviewable as a case expands from one account or party to a wider connected group. Investigators can expand hop by hop under policy controls, such as which relationship types are allowed, which links meet confidence thresholds, which time windows apply, and how many hops are permitted, until they confirm the exposure chain or reach the step limit. The returned path shows exactly how the exposure accumulates and supports the escalation rationale.
TigerGraph can run these traversals and path patterns directly in the database, which avoids exporting the logic to another layer.
Next steps to take
Start with policy, not tooling. Define what “exposure through connections” means in your program before you try to automate it.
- Write down the relationship types your program treats as exposure-relevant. Examples include ownership, control, beneficial ownership, shared addresses, shared devices, shared routing infrastructure and intermediary involvement.
- Set clear hop limits for review. Decide how far the workflow should expand for triage versus escalation, then apply those limits consistently.
- Require path evidence in every escalation. The output should show the chain of connections used, not only a score or a label, so a second reviewer can reproduce the same view.
- Keep language disciplined in case notes. Multi-hop exposure supports prioritization and review. It does not prove a violation on its own.
If your team still has to reconstruct connection chains manually across tools, the gap is not data. The gap is visibility and repeatability. Graph workflows are designed to reveal complex patterns of connection and return the path as reviewable evidence.
When sanctions screening requires multi-hop traversal with consistent, reviewable path outputs at investigation depth, include TigerGraph in the evaluation and benchmark it against your current screening workflow. The practical test will be whether the platform can return the path evidence your reviewers keep asking for, without manual stitching. Reach out to learn more!
Frequently Asked Questions
1. What is Indirect Sanctions Exposure in Financial Crime Compliance?
Indirect sanctions exposure occurs when an entity is not directly listed on a sanctions list but is connected to a sanctioned entity through relationships such as ownership, intermediaries, shared infrastructure, or transaction chains. These exposures often appear one or more steps away from the entity being reviewed, making them difficult to detect using traditional direct-name screening methods.
2. Why do Traditional Sanctions Screening Systems Miss Indirect Exposure?
Traditional sanctions screening systems focus on direct matches between names, identifiers, or entities and official sanctions lists. While this approach identifies obvious matches, it does not reveal exposure that exists through connected relationships such as intermediary companies, ownership layers, or repeated counterparties. Detecting these risks requires analyzing how entities connect across the broader network.
3. What are Connection Paths in Sanctions Investigations?
Connection paths are the sequence of relationships linking one entity to another through multiple steps. For example, a company may connect to a sanctioned entity through an intermediary supplier or beneficial ownership chain. Identifying and reviewing these paths helps compliance teams understand how exposure arises and provides explainable evidence for escalation decisions.
4. How does Graph Analysis Help Detect Sanctions Exposure Through Indirect Connections?
Graph analysis models entities and their relationships as a connected network. Investigators can traverse the network step by step to identify indirect links between entities and sanctioned parties. This approach allows compliance teams to detect exposure that emerges through ownership structures, intermediaries, or transaction chains that would be difficult to identify using record-based analysis alone.
5. Why are Explainable Relationship Paths Important for Sanctions Compliance Investigations?
Explainable relationship paths provide clear documentation showing how an entity connects to potential sanctions exposure. Instead of relying on scores or automated alerts alone, investigators can review the chain of relationships that created the exposure. This path-based evidence helps compliance teams justify escalation decisions, maintain audit-ready documentation, and support regulatory reviews.