

Guard Against Cybersecurity Threats in Real-time With TigerGraph
Cost of Cybersecurity Attacks
Average Cost of Cyber Attack
Increase In Insider Threats
Businesses Face the Constant Threat of Cybersecurity Attacks
Cybersecurity attacks were estimated to cost an astounding $45 billion in 2018. The Internet Society’s Online Trust Alliance (OTA), which identifies and promotes security and privacy best practices that build consumer confidence in the Internet, released its Cyber Incident & Breach Trends Report, which found the financial impact of ransomware rose by 60%, losses from business email compromise (BEC) doubled, and cryptojacking incidents more than tripled, all despite the fact that overall breaches and exposed records were down in 2018.
Network and security vendors need a more accurate and timely solution to protect their customers. Security is only effective if it uses accurate and timely threat data.
Read More
Legacy Approaches Are Ill-Suited for Deflecting Cybersecurity Threats


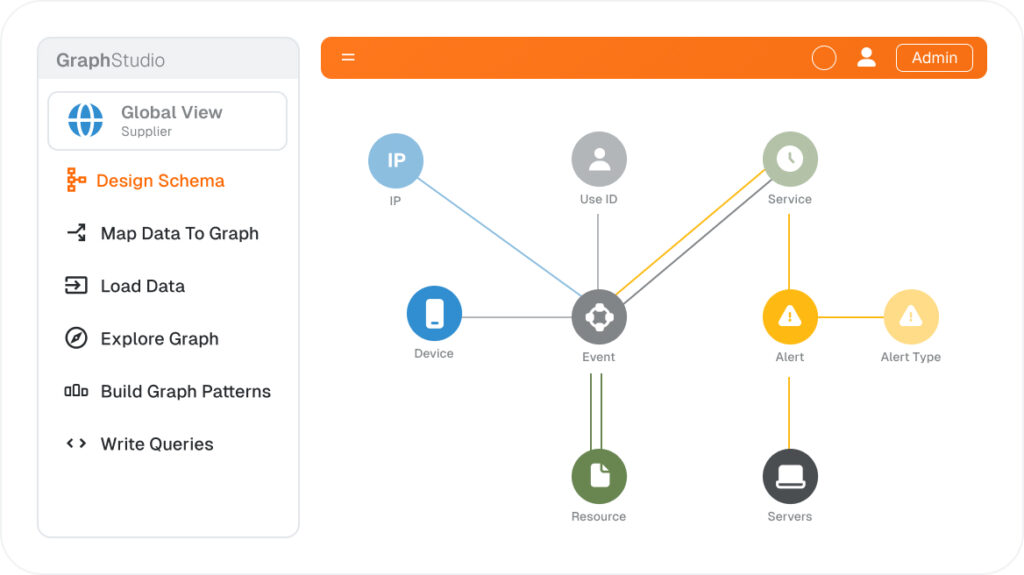
Database for Cybersecurity?
Graph Databases Are an Ideal Way to Detect Cybersecurity Threats
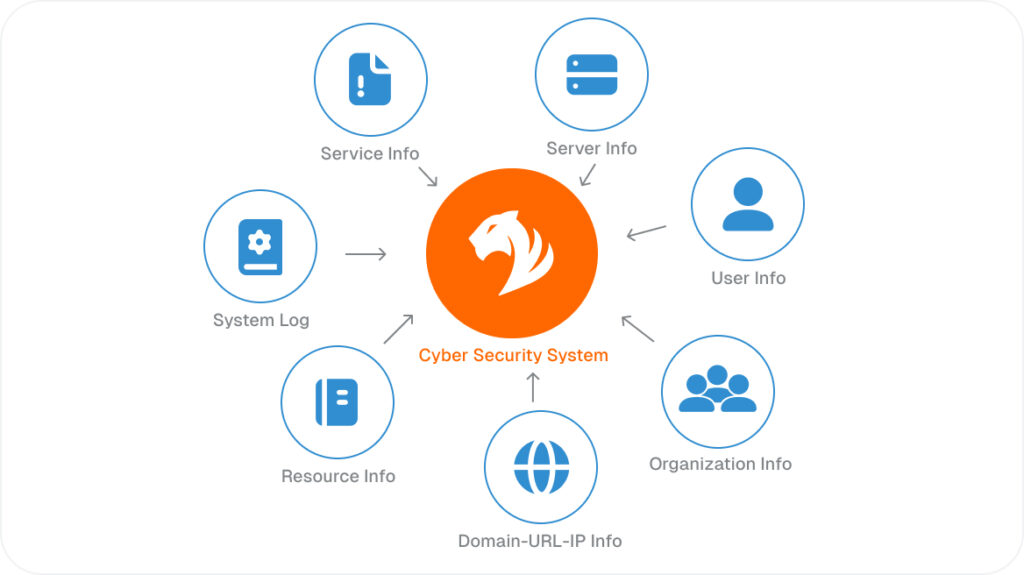
Graph Databases Can Fight Cybersecurity Threats in Multiple Ways
FAQ
Description
