How to Keep Correspondent Banking Escalations Reviewable with Chain Evidence
Many escalation decisions in correspondent banking are unknowingly made in the dark, as they often depend on relationship chains that are not visible in the transaction record. Teams need a way to retrieve a broader chain quickly and preserve it as evidence so reviewers can reach the same conclusion consistently. Graph supports efforts to create a more efficient and transparent workflow.
Key takeaways
- Nested exposure is easier to evaluate when teams can see the full chain of banks and intermediaries involved, not only the transaction endpoints.
- Correspondent banking exposure often appears through repeated routing choices and recurring use of the same intermediaries.
- Exposure definitions should remain program-defined. If scoring is used, escalation should still include the chain evidence that establishes the connection.
- Chain evidence matters because exposure often accumulates across multiple relationship steps, not within a single transaction field.
What Correspondent Banking Reviews Assess
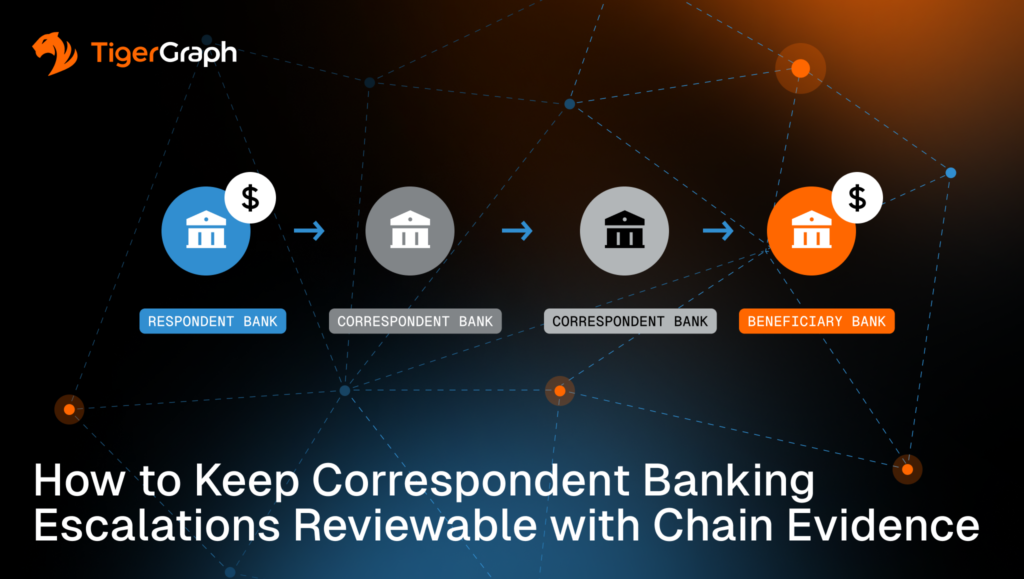
A payment record typically shows the sending and receiving institutions, but it does not always show every bank and intermediary involved in moving value from start to finish.
A correspondent bank provides services that allow another bank to complete cross-institutional payments. The respondent bank is the institution using those services. In practice, a single payment may pass through several correspondent and respondent relationships before reaching its destination.
Correspondent banking reviews evaluate these payments as they move through multiple financial institutions. The focus is not only on the named counterparty on the transaction record, but also on the institution chain that enabled the payment route.
Although this multi-institution structure is expected, the operational challenge appears when review workflows cannot reliably reconstruct that structure during escalation. This is where things break down.
Where Escalation Workflows Break Down
Many correspondent banking reviews slow down at the same point. The transaction shows one endpoint, but the escalation decision depends on how exposure builds across the broader routing chain.
At that stage, the question is no longer whether exposure exists in general, but how the program defines exposure and whether the workflow can return the evidence required to support that definition.
Exposure boundaries are set by program policy. Different institutions draw them differently based on risk appetite, regulatory expectations, and internal controls. One exposure category that frequently depends on chain visibility is nested relationship exposure.
Understanding Nested Relationship Exposure
Nested relationship exposure refers to risk that does not sit on the transaction itself, but emerges from how the institutions involved are connected behind the scenes. It is program-defined exposure that sits within the relationship chain rather than at the transaction endpoint.
It can appear when a respondent bank is connected to higher-risk parties through nested account structures, downstream institutional relationships, or repeated routing through the same intermediary chain.
When workflows cannot return that chain as evidence, teams often reconstruct it manually across systems. This increases review time and introduces inconsistency, especially as review volumes scale.
This is a workflow constraint, not a detection failure. Reviews stall when teams cannot expand context in a controlled way and preserve the connecting chain as reviewable evidence.
How Nested Exposure Shows Up in Practice
This constraint shows up in the following review patterns:
- The endpoint is not the full story
A transaction lists one bank as the counterparty, but routing depends on additional banks and relationships behind the scenes. - Indirect exposure through nested relationships
A respondent relationship, nested account structure, or layered institutional chain places activity closer to higher-risk entities than direct screening suggests. - Repeated use of the same chain
A single instance may be explainable. Repeated use of the same intermediary chain or routing corridor across related activities carries more weight for review.
None of these patterns proves wrongdoing. They support prioritization and investigation when exposure is defined under program policy and the supporting evidence remains reviewable.
What Graph Analysis Adds to Nested Exposure Review
Graph analysis supports this workflow by treating relationships as first-class data and returning the connecting chains that show how exposure was established.
This enables several operational capabilities:
- Flexible depth
Reviews often begin with one transaction or entity and expand until the routing chain makes sense under policy. The required depth is not always known in advance. - Chain-based review
Teams can review the full institution and intermediary chain as a single connected picture instead of stitching fragments across systems. - Consistent decisions
When relationship logic is expressed consistently, analysts see the same definition of connected exposure across queues. - Reviewable evidence
The workflow preserves the chain used for escalation so a second reviewer can reproduce the same view.
Scoring, weighting, thresholds and escalation criteria remain program-defined. Even when scoring is used, the workflow must return the chain evidence reviewers need to inspect.
How TigerGraph Fits
As mentioned, correspondent and nested exposure reviews break down when teams cannot keep the full relationship chain in view. Investigators reconstruct institutional context manually, and reviewers approve escalations without a consistent evidence trail.
TigerGraph supports this workflow by enabling controlled relationship expansion, also known as traversal. Traversal starts from one bank, account or transaction and follows its connections step by step through related institutions and intermediaries. The system moves along actual relationships rather than reassembling them on the fly, and it preserves the path taken as part of the output.
This matters because investigators rarely know in advance how many relationship steps are required. Sometimes exposure appears one link away. In other cases, it only becomes clear after several “hops” or steps through correspondent and respondent relationships. Traversal supports that variable depth while keeping the full chain intact and reviewable.
As a result, teams can define exposure-relevant relationship logic within program policy, apply it consistently across cases, and provide evidence explaining why the activity was treated as a nested exposure rather than an isolated transaction.
Next steps to keep this operational
Start with what your program needs to defend.
- Define nested exposure in program terms. Document which relationship types matter and how far workflows should expand for triage versus escalation.
- Require chain evidence in escalations. Case notes should show the institution and intermediary chain used, not only a label or score.
- Standardize the review view. Analysts should see the same chain output across queues to prevent decision drift.
- Pressure-test with real cases. Select recent correspondent-related escalations and confirm whether your workflow can return the full chain without manual reconstruction.
If your current program cannot do this, consider adding TigerGraph to your workflow to return the evidence reviewers require.
Frequently Asked Questions
1. What is Nested Exposure in Correspondent Banking Compliance?
Nested exposure occurs when risk emerges through the chain of correspondent and respondent banking relationships rather than from the transaction endpoint itself. A payment may appear routine on the surface, but the routing path can involve intermediary banks or nested account structures that bring the activity closer to higher-risk entities. Understanding these relationships helps compliance teams assess the full institutional context behind a transaction.
2. Why are Correspondent Banking Escalation Decisions Difficult to Explain?
Escalation decisions can be difficult to explain when investigators cannot easily reconstruct the full chain of institutions involved in a payment route. Transaction records typically show only the sending and receiving parties, while the intermediary banks that facilitated the transfer may not be immediately visible. Without the full relationship chain, compliance teams may struggle to provide consistent evidence supporting escalation decisions.
3. What is Chain Evidence in Correspondent Banking Investigations?
Chain evidence is the documented sequence of institutions, accounts, or intermediaries that connect a transaction to potential exposure. Instead of relying on isolated alerts or risk scores, chain evidence shows the full relationship path linking entities within the payment route. This evidence allows investigators, reviewers, and auditors to understand how exposure was identified and why the case was escalated.
4. How does Graph Analysis Help Detect Risk in Correspondent Banking Networks?
Graph analysis models banks, accounts, and transactions as a connected network of relationships. By traversing these connections step by step, investigators can reconstruct payment routes across correspondent and respondent institutions. This approach helps reveal indirect exposure, repeated intermediary chains, and routing patterns that would be difficult to detect using transaction records alone.
5. Why are Explainable Relationship Chains Important for Correspondent Banking Compliance?
Explainable relationship chains allow compliance teams to show exactly how exposure was identified within a payment network. When an escalation occurs, investigators can present the sequence of institutions and intermediaries involved rather than relying solely on automated risk scores. This improves consistency across investigations and provides the clear documentation required for internal review, audit, and regulatory oversight.