Proximity Risk in KYC and KYB: Why Second-Degree Connections Change the Outcome
Most know-your-customer (KYC) and know-your-business (KYB) reviews focus on the entity being evaluated. The core question is straightforward. Does this customer, business or counterparty present unacceptable risk?
That framing works when risk is contained within the entity itself. It becomes incomplete when relevant exposure sits just outside the entity under review.
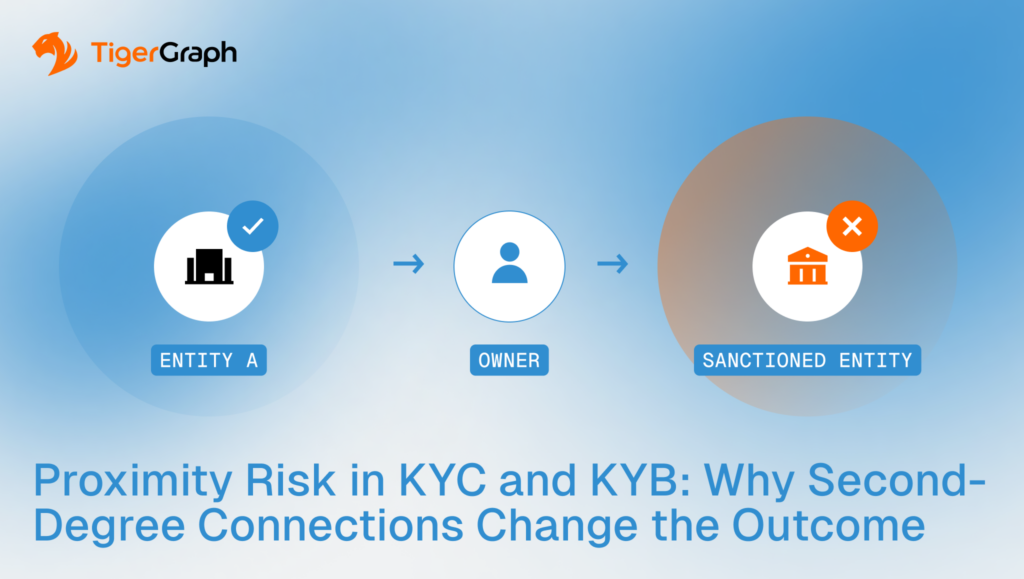
This is known as proximity risk. In these cases, risk does not originate solely from the subject, but from how the subject is connected to others. Identifying and reviewing that nearby exposure requires visibility beyond direct attributes.
Key takeaways
- Risk does not always sit on the entity under review. It often sits in the surrounding network.
- Second-degree connections can materially change escalation decisions, even when first-degree checks pass.
- Graph-based workflows support proximity review by returning connected entities and the relationship paths that justify review.
Why Proximity Matters in Identity Reviews
Proximity risk describes situations where exposure emerges through relationships rather than direct attributes. An entity may appear acceptable in isolation, yet be closely connected to other entities that elevate concern.
KYC and KYB processes are designed to assess direct evidence. This typically includes identity attributes, ownership information, sanctions and watchlist screening, and transaction history. These controls are effective for many cases.
Proximity complicates this picture.
An entity can meet baseline requirements while being closely connected to entities that do not. These connections may involve shared ownership, shared infrastructure, repeated counterparties or indirect exposure through intermediaries.
When reviews stop at direct relationships, programs risk treating materially different cases as equivalent. Over time, this leads to inconsistent outcomes and decisions that are difficult to explain to QA teams, auditors, and regulators.
How Proximity Risk Shows Up in Practice
Proximity risk tends to surface in a small set of recurring review patterns.
Indirect exposure through shared relationships
A business may have clean documentation and ownership yet be closely connected to another entity with elevated risk. The connection itself is not prohibited, but it changes how the case should be evaluated.
Second-degree connections that repeat across cases
The same intermediaries, service providers, or counterparties appear across multiple entities. Individually, none may trigger escalation. Collectively, they form a pattern that warrants review.
Escalation decisions that vary by reviewer
Some reviewers account for nearby exposure, but others do not. This results in inconsistent outcomes that are difficult to defend after the fact.
None of these scenarios requires assuming intent. They require understanding context. That context often sits one relationship step beyond what standard checks capture.
What Second-Degree Connections Add
Second-degree connections are entities linked to the subject through one intermediate relationship.
In practical terms, this expands the review question. Not only “Who is this entity connected to?” but also, “Who are those connections connected to?”
This additional step can surface:
- Exposure that does not appear in first-degree checks
- Concentration risk that only becomes visible when the review scope expands
- Patterns that recur across cases, even when individual entities appear acceptable
The challenge is applying this broader context consistently, without overwhelming investigators or expanding the scope arbitrarily.
What Connected Analysis Adds
Connected analysis supports proximity review by making scope explicit and repeatable.
It defines how far the review should extend.
Programs can specify whether proximity review stops at one step, two steps or varies by typology. This prevents ad hoc expansion during investigations.
It preserves relationship paths as evidence.
When proximity influences an escalation, reviewers can show exactly how the entity is connected to the source of concern.
It separates structure from judgment.
The graph returns connected context. Risk decisions remain governed by policy and human review.
This distinction is critical for consistency and auditability.
Applying Proximity Risk in KYC and KYB Workflows
Proximity risk is the awareness of when proximity should influence a decision.
Programs typically benefit from clearly defining which relationship types justify proximity review. Ownership, control relationships, intermediaries, shared infrastructure and repeat counterparties often matter more than casual associations.
Proximity can also affect escalation thresholds. It may not trigger escalation on its own, but it can change how marginal cases are treated.
Operationally, teams benefit from:
- Defining which relationships trigger proximity review
- Setting clear depth limits for expansion
- Requiring connection paths when proximity influences escalation
- Monitoring consistency across reviewers and cases
When proximity affects a decision, the connection path should be part of the case record. Without this discipline, proximity risk is applied inconsistently.
How TigerGraph Fits the Workflow
The operational challenge is efficiently reviewing second-degree connections and explaining why they matter.
Graph workflows support this by storing relationships directly and returning connection paths as part of the output. TigerGraph supports proximity review by enabling:
- Multi-hop (multi-step) traversal across identity, ownership and transactional relationships
- Repeatable proximity queries with consistent scope
- Evidence paths that support QA, escalation, and audit review
The system does not decide risk. It provides the context that underlies decisions.
KYC and KYB programs are strongest when similar cases produce similar outcomes. Proximity risk is one of the most common reasons that consistency breaks down. Often, the difference is not the entity under review, but how far the reviewer looked.
If your current program is not supporting consistent, traceable results, connect with TigerGraph and we’ll help you rethink your workflow.
Frequently Asked Questions
1. What is Proximity Risk in KYC and KYB Investigations?
Proximity risk refers to situations where an entity appears compliant on its own but is closely connected to other entities with elevated risk. In KYC and KYB reviews, risk may arise through shared ownership, common intermediaries, repeated counterparties, or shared infrastructure. Evaluating these nearby connections helps investigators understand whether risk exists just outside the entity being reviewed.
2. Why can Traditional KYC and KYB Reviews Miss Hidden Risk?
Traditional KYC and KYB reviews primarily evaluate the entity itself using attributes such as ownership records, sanctions screening, and transaction history. While these checks are essential, they often stop at direct relationships. Hidden risk can remain undetected when exposure sits in nearby entities that are connected through intermediaries or shared networks.
3. What are Second-degree Connections and Why do They Matter in Risk Analysis?
Second-degree connections are entities linked to the subject through one intermediary relationship. For example, a business may be connected to a supplier, which in turn is linked to another entity with elevated risk. Evaluating second-degree connections helps investigators identify indirect exposure, recurring relationship patterns, and network structures that may not appear in first-degree checks.
4. How does Graph Analysis Improve Proximity Risk Detection?
Graph analysis models entities and their relationships as a connected network. This allows investigators to explore relationships across multiple steps and identify indirect connections that may influence risk decisions. By traversing the network, teams can detect patterns of shared ownership, intermediaries, or counterparties that would be difficult to identify using traditional record-based analysis.
5. How do Graph-based Workflows Improve Explainability in KYC and KYB Reviews?
Graph-based workflows improve explainability by preserving the relationship paths that connect entities. When proximity risk influences a decision, investigators can show exactly how the subject is linked to another entity through ownership, transactions, or intermediaries. This path-based evidence helps ensure consistent decisions and provides clear documentation for compliance, audit, and regulatory review.