Cybersecurity Defense-in-depth and Graph Analytics
- Blog >
- Cybersecurity Defense-in-depth and Graph Analytics
Cybersecurity requires proactive defenses that will find and deal with advanced security threats. These systems can stop the cyber-attacks that your organization will almost certainly encounter. This protection provides multiple and duplicative defensive solutions and anticipates counter cyber actions.
Cybercriminals use complex tools to attack your system. Thus, cybersecurity takes measures to avert these attacks. Cybersecurity defense strategies are aimed at responding to and preventing such cyber-attacks. Additionally, the system is set to disrupt them if they do happen.
What is Defense-in-depth?
Defense-in-depth is a commonly used term in the cybersecurity industry that has many definitions with subtle variations, but all sharing many of the same common themes. Defense-in-depth is a cybersecurity or information security approach involving a series of systems, mechanisms, and controls layered together to protect your organization’s network, computer systems, and the data contained within those resources.
Defense-in-depth Strategy
As organizations move into multi-cloud systems, a hands-on approach will enable you to anticipate cyber-attacks and disrupt them when they happen. These attacks could take a toll on your IT resources and your finances. In addition, their effect could tarnish your brand name irreparably.
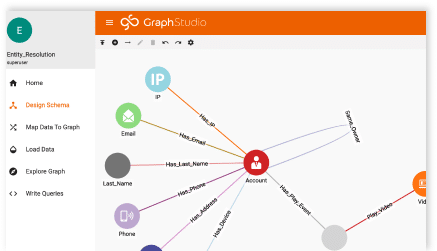
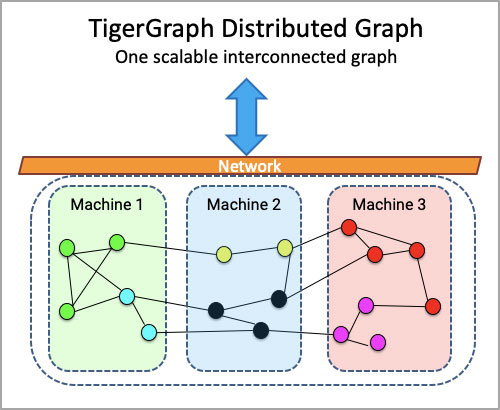
However, you will strengthen your company with defense-in-depth and conduct your day-to-day business despite sophisticated malware, in the process strengthening customer trust and improving shareholder value. One of the most critical pieces of your defense-in-depth strategy is the combination of visualization and analytics that allows you to proactively respond in an automated fashion to the threats as they are identified. Graph databases give you the capability to use the connected data from all of your security stack tools to achieve this goal.
The misconception that a breach can be prevented is just that: a misconception. If an experienced bad actor wants to get into a network for the sensitive data contained within, they will find a way in. The best action that you can take is to identify this act as quickly as possible to prevent any damage or sensitive data loss. TigerGraph will enable the in-database machine learning and the deep link analytics to proactively identify threats that a single tool may miss.
Your defense-in-depth strategy includes controls to protect your business networks technical, administrative, and physical aspects. Here we take a look at how it works:
Administrative Controls
Defense-in-depth measures control the administrative aspects of your business. These include policies and procedures directed at the organization’s employees and labeling sensitive information as ‘confidential.’ Login systems for your employees are also included. The use of PAM (Privileged Access Management) solutions along with true graph analytics will help control who is getting into what systems and watch for any anomalous privilege escalations for user accounts.
Technical Controls
Defense-in-depth measures to control malware refer to the hardware you put in place to protect network systems and resources. You can also have software and network firewall appliances or an antivirus program. The connected data analytics as well as the algorithms used to automate the threat analysis and threat hunting will enhance any SOC team’s tool chest.
Physical Controls
These are defense-in-depth measures that will prevent physical access to your IT systems. These should include security guards, locked doors, and alarm systems.
Here are other defense-in-depth security layers added to the first layer. These extra measures will ensure a cyber attacker won’t get deep into your systems if they get past the first line of defense.
Access Measures
Access measures have biometrics, timed access pins, VPN, and controlled authentication. Access to any data will need access codes. The use of IAM to the fullest will enable true multi-factor authentication to ensure proper validation of users and the systems they use to access sensitive systems or information. Using the proper graph database technology will ensure you can connect these events and alerts with the data from other security stack tools to best react to threats.
Perimeter Defenses
Network perimeter defenses comprise intrusion detection systems that alert when someone tries to access the perimeter. They include prevention systems and firewalls.
Monitoring Prevention
Preventing and monitoring network attacks include auditing network activity, logging, sandboxing vulnerability scanners, and security awareness training. Along with these monitoring systems, the use of TigerGraph’s true Deep Link Analytics, Connected Data, and In-database Machine Learning technology with its massively parallel processing capabilities will give you the edge you need.
Workstation Defense Mechanisms
Workstation defense mechanisms include anti-spam and antivirus software. They deal with spam and viruses directly.
Data Protection Mechanisms
Among data protection methods, hashing, data-at-rest encryption, and secure data transmission are at the forefront. In addition, there are encrypted backup systems to enhance security a step further. Using the logs, SEIM data, XDR, NDR, EDR, and EPP data sources, as well as monitoring other system data in a single graph database, will ensure you are protecting the data you have through proactive Defense-in-Depth strategies.
Using Defense-in-Depth Solutions
Use companies that provide defense-in-depth security solutions to provide a complete suite of these defenses for your organization. They will work on all the multiple lines of defense to make sure your data and network are safe from malware and security issues.
While there is no way of avoiding cyber-attacks, there are ways of mitigating the risks and preparing your company in advance for when they come. Data security solution companies will help keep your data safe. They will also ensure that your network is protected again. The use of graph databases like TigerGraph gives you the edge you need against the adversaries you’re sure to face today.