Ransomware Threats Are on the Rise – What Can You Do?
- Blog >
- Ransomware Threats Are on the Rise – What Can You Do?
After reviewing research from many companies preparing to write this article, it became very clear that the threat level for enterprise organizations is on the rise. This shouldn’t come as any surprise. The number of bad actors, attackers, insider threats, and much more has been plaguing businesses for years. Since the first discovery of ransomware in 2006, the security industry has been on the ropes. To make matters worse, over the past year to eighteen months, ransomware attackers have become even more aggressive and lethal.
The number of actual targeted ransomware attacks is much higher once you figure in all of the unconfirmed and unreported attacks. Confirmed attacks from known targeted ransomware families are a sample of the overall number of attacks. You also have to consider that many targeted ransomware attacks are halted before they can do any damage thanks to proper alerting and defensive measures. This in turn causes the attack to not be attributed as ransomware.
When you consider that most targeted ransomware operators recompile their ransomware for every new attack, multiple variants of each kind of ransomware typically exist. Because of this fact, the variant of the ransomware used in an attack may be blocked by generic or machine learning-generated detections rather than a detection linked to that ransomware family. This will also skew the number of identified attacks.
Ransomware Identification – An Enterprise Necessity
Identifying ransomware threats is no longer a “nice to have” capability. Finding these threats as early as possible in the kill chain is critical to your cybersecurity battle against ransomware as well as every other outsider or even insider threat. When you look at the MITRE ATT&CK framework, the tactics and techniques of Reconnaissance, Initial Access, Privilege Escalation, Credential Access, and Lateral Movement are the phases that should alarm you enough to take immediate action. Noticing these anomalies, user behavior patterns, and unusual actions taken in your network can be the early warning signs you need to stop a ransomware attack before execution and lockdown.
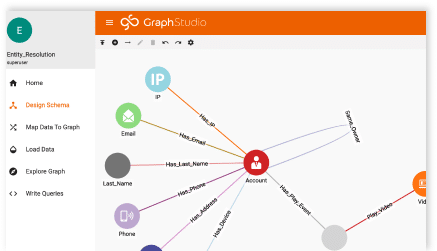
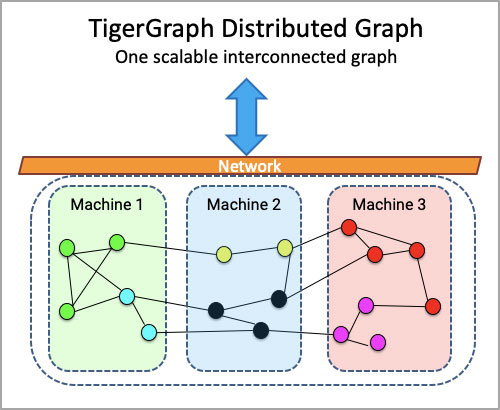
TigerGraph’s graph platform will give you the ability to use the connected data from all of your disparate tools and data sources to quickly identify threats and further your SOC team’s threat hunting practices.
Learning from Past Attacks
The attack against Colonial Pipeline in the U.S. in May 2021 caused significant disruption and prompted concerns about the nation’s fuel supplies. In the same month, an attack on Ireland’s national health service, the Health Service Executive, forced it to cancel thousands of appointments and initiate a recovery operation that took a very long time to conclude. Both of these attacks, and countless others, could have been mitigated by better visibility into the victim organizations’ data and systems.
Everyone in the security industry accepts that lack of visibility caused by disparate tools not sharing alert and event data can cause security analysts to suffer from significant alert fatigue. Your SOC and NOC analysts need a solution that brings all of the data together with automated deep link analytics, algorithms that allow for customization of queries to find commonalities and relationships using In-database Machine Learning, and most of all, provide the correlation of events that will enable the reduction of false positives and false negatives.
TigerGraph offers in-database machine learning that enables you to quickly identify and potentially stop these attacks before the payload is deployed or even post-deployment but before execution. In the majority of attacks, the bad actors do not immediately execute the attack; they drop the ransomware payload and allow it to spread through daily and weekly system backups, ensuring a more robust attack.
Identification Is the Key
As I mentioned before, identifying an attack as early as possible – before or soon after deployment – is the crucial goal that organizations must achieve. Even with the government and law enforcement crack down on ransomware gangs over the past few years, threat actors remain undeterred, and the cost of these attacks are on the rise. The rise of fees or ransom paid is not as much as the cost of mitigation and cleanup.
If you can identify a threat through connected data visibility with a graph database, then your chances of reducing that cost of mitigation and preventing the need to pay the ransom become much more realistic.