Common Cyber-attacks in the U.S.
Cyber-attacks have risen worldwide, especially since the COVID-19 pandemic struck, with an increased number of companies suffering data breaches. According to Business Wire, 81% of organizations globally have experienced an…
The Intersection of Learning, Knowledge, and Language
This is an abbreviated and edited version of a presentation by Dan McCreary, Distinguished Engineer - Advanced Technology Collaborative at Optum, a division of UnitedHealth Group, during the Graph +…
Fireside Chat with Google, Capgemini, and TigerGraph
This is an abbreviated version of a conversation between Philip Moyer, Vice President, Strategic Industries at Google Cloud, Sankar Krishnan, Executive Vice President, Industry Head, Banking & Capital Markets at…
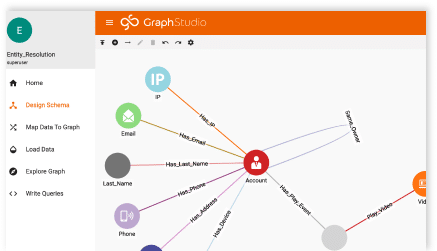
Cybersecurity Defense-in-depth and Graph Analytics
Cybersecurity requires proactive defenses that will find and deal with advanced security threats. These systems can stop the cyber-attacks that your organization will almost certainly encounter. This protection provides multiple…
Accelerated Graph Analytics to Answer Complex Business Questions
This is an abbreviated and edited version of a presentation by Bob DeCarlo, General Manager, Global Accounts, Financial Services, Bank of America at HPE, and Delvon Jones, Director and Chief…
Driving Operational Excellence with Real-time Data Operations in Retail
Before we start, what do we mean by ‘realtime data operations’ in retail supply chain? Retail supply chains are typically very complex networks of many people, businesses, products, and both…
Implementing a Biomedical Knowledge Graph Using BERN2 and TigerGraph
This blog is a reprint of an article published by the author on Medium.com on March 15, 2022.Do you know how to construct a biomedical knowledge graph using TigerGraph and…
- Go to the previous page
- 1
- …
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- …
- 34
- Go to the next page